There is a lot of constant improvement being executed by the MCS team at Citrix, the release cadence is impressive and the feature enhancements significant. I spend a lot of time in Microsoft Azure with Citrix Cloud with a lot of happy customers. I thought it would be worthwhile keeping a rolling tally of new features with MCS and how it relates to Azure, so that we don’t lose sight of how much value add is provided.
I will do my best to maintain this list as and when features come out, as well as some commentary around their value where I can.
It is important to be across the options when designing your delivery platform on Azure, many changes have a direct implication on the ongoing operational costs associated with running workloads on/in Azure, as well as availability and global deployment options. Looking at what we have now, vs what was available 12 months ago, many designs and deployments would look remarkably different.
July 2024
Azure has increased the maximum count of replicas for a gallery image single version to 100. With this limit increase, you can now set the property SharedImageGalleryReplicaMaximum to a maximum value of 100 while creating an MCS machine catalog using the Azure Compute Gallery image.
An Images node is now available in Web Studio, letting you prepare an MCS image (prepared image) from a single source image and deploy it across various MCS machine catalogs. This node facilitates complete image lifecycle management, enabling you to create image definitions, versions, and catalogs.
Images prepared using this node can only be used in Azure and VMware environments. Alternatively, you can also create catalogs with prepared images using the Machine Catalogs node.
With this feature, if you configure the master VM with nested virtualization enabled, then all VMs in the MCS machine catalog created using that master VM have nested virtualization enabled. This feature is applicable to both persistent and non-persistent VMs. You can update an existing MCS machine catalog and existing VMs to have nested virtualization through image update.
Currently, only Dv3 and Ev3 VM sizes support nested virtualization.
You can create an MCS machine catalog of Azure VMs with on-demand capacity reservation using a machine profile (VM or template spec). This feature is applicable to persistent and non-persistent machine catalogs. You can update an existing machine catalog and existing VMs to have or remove on-demand capacity reservations.
For more information on Azure on-demand capacity reservation, see the Microsoft documentation On-demand Capacity Reservation
You now have the option to update the memory and disk cache size of the write-back cache, when Machine Creation Service (MCS) Storage Optimization (MCSIO) is enabled, after the catalog is created for MCS catalogs.
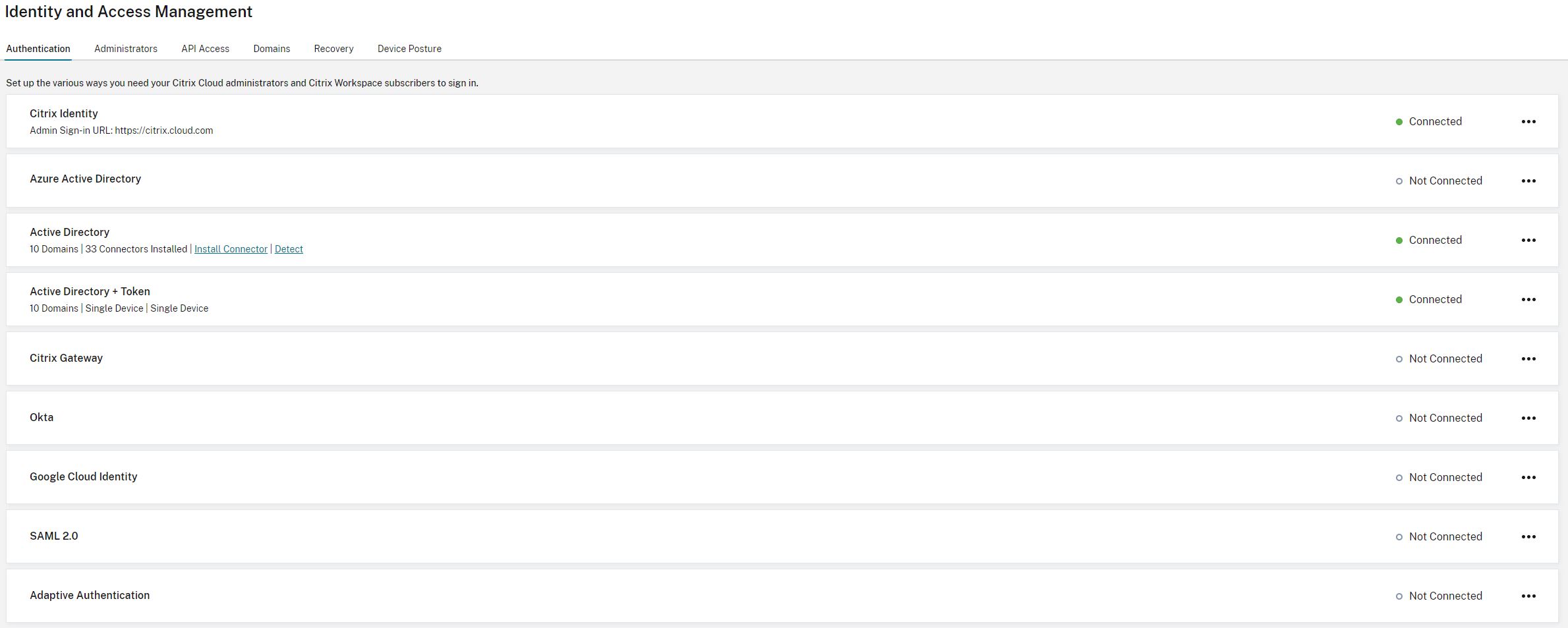
Citrix enhanced the Enable Azure AD joined device management option for greater flexibility. Previously, you had to sign in to Azure and allow Citrix to assign the Cloud Device Administrator role to the connection’s service principal on your behalf. This design worked only when your Azure account had permission to grant this role.
With this enhancement, if your Azure account doesn’t have the required permission, you can now choose Don’t sign in to Azure when enabling Azure AD joined device management. This allows you to manually assign the role to the connection’s service principal in the Azure portal.
June 2024
Previously, to change the subnet settings of a machine catalog, you had to delete and recreate it. With this feature, you can now achieve the same functionality by editing the catalog. Note that only new virtual machines created under the catalog will be on the newly associated subnets. This enhancement reduces the need for catalog deletion and associated tasks.
I know, it’s not MCS, but it still falls under “Provisioning” so I am adding it.
Previously, when creating Azure catalogs using Full Configuration, you had to create the resource groups using PowerShell commands. With this feature, you can now seamlessly create a resource group as part of catalog creation in Web Studio. This enhancement simplifies the overall creation workflow.
May 2024
You now have the option to support hibernation for Azure machine SKUs that support GPU
Azure confidential VMs provide a strong, hardware-enforced boundary to help meet your security needs. With the Full Configuration user interface, you can now create and manage confidential VMs on Azure
I am going to dump this one here as even though it’s not provisioning, there is an obvious dotted line towards it, and this feature is really, really cool.
April 2024
You can now change the disk encryption in Azure virtualization environments. You can do the following:
- Create an MCS machine catalog with a disk encryption set (DES) that is different from the master image DES.
- Change the disk encryption type from one DES key to another DES key of an existing MCS machine catalog and existing VMs.
- Update an MCS machine catalog and VM that was not previously CMEK enabled to have customer-managed encryption key (CMEK) encryption (DES), disk encryption at host, or double encryption.
- Update an existing MCS machine catalog and VM to be non-encrypted that was previously encrypted.
- Enable disk encryption with private endpoint (an MCS machine catalog that used a host connection enabled with
ProxyHypervisorTrafficThroughConnector).
You can now modify the page file settings of the newly added VMs to an existing catalog without updating the master image. This is currently an Azure only feature.
To modify the page file settings, you need VDA version 2311 or later. You can modify the page file settings using the PowerShell commands.
March 2024
Previously, to change the subnet settings of a machine catalog, you had to delete and recreate it. You can now achieve the same functionality by editing the catalog. Note that only new virtual machines created under the catalog will be on the newly associated subnets. This enhancement reduces the need for catalog deletion and associated tasks
With Full Configuration, you can now update a wider range of settings for MCS-provisioned Azure VMs through machine profiles, which include:
- Machine size
- License type
- Availability Zone
- Dedicated Host Group ID
After you update the machine profile, Full Configuration compares the current settings with the new ones. If differences exist, you’ll be prompted to confirm which to apply. This design ensures transparent and efficient VM setting updates.
For Azure VMs provisioned using Machine Creation Services (MCS), you can now change their write-back cache (WBC) properties using Full Configuration, such as Disk cache size, Memory cache size, and Enable storage cost saving.
In addition, when you select a new machine size or machine profile for those VMs, Full Configuration validates WBC settings to prevent conflicts, such as exceeding the memory limit of the new selection. If conflicts occur, you’ll be prompted to re-configure WBC settings.
February 2024
Another example of the product teams listening to requests. You can now view the following image information through the Template Properties of the machine catalog:
- Operating system
- Machine identity service
- Machine Creation Service storage
- Filepath for
pagefile.sys for Azure deployments
This enhancement provides better clarity on the image information and ensures that the administrators have all the information about the machine catalog in one place.
In Azure environments, previously, the Disk Encryption Set ID (DES ID) of an MCS machine catalog was derived from a machine profile or custom properties. With this feature, a machine catalog can also derive the DES ID from the master image to encrypt all the disks of the VMS in a catalog.
When you migrate from on-premises configuration to a cloud site, or from your cloud configuration to another cloud site, the orphaned resources aren’t detected correctly because of the old site id tag. With this feature, using a PowerShell command, you can update the MCS site id tags of a persistent catalog, after migration so that orphaned resources can be detected correctly. Currently, this feature is applicable to Azure.
With this feature, you can now validate configuration settings before creating an MCS machine catalog using the parameter -validate in New-ProvScheme command. After you run this PowerShell command with the parameter, you get an appropriate error message if there’s an incorrect parameter used or a parameter has conflict with another parameter. You can then use the error message to resolve the issue and successfully create an MCS machine catalog using PowerShell.
Currently, this feature is applicable to Azure, GCP, and VMware virtualization environments.
For anyone who has played with automating Catalog creations, this is a welcome feature.
Azure Spot VMs allow you to take advantage of Azure’s unused computing capacity at significant cost savings. However, due to its eviction policy, Azure Spot VMs are good for only some non-critical applications and desktops.
With this feature, you can create an MCS machine catalog of Azure Spot VMs using a machine profile (VM or template spec). You can update an existing catalog to have Azure Spot VMs as the newly created VMs or switch to have standard Azure VMs. You can also update existing VMs to be Azure Spot VMs.
Be careful with Spot VMs.
In Azure environments, MCS now supports capturing of diagnostic settings on VMs and NICs from a machine profile while creating or updating an MCS machine catalog, or updating existing VMs. With this implementation, the diagnostic data can be seamlessly transmitted to designated Azure destination endpoints, such as Log Analytics workspaces or Event Hubs, for in-depth analysis and visualization.
With this feature, you can manage the configuration versions of a machine catalog using PowerShell commands. Each configuration change using the Set-ProvScheme results in a new configuration version. You can:
- See the list of versions.
- Use any previous version to update a machine catalog.
- Manually delete a version if it isn’t used by a VM.
- Change the number of maximum versions to be retained by a machine catalog.
January 2024
Previously, Full Configuration set the Azure catalogs’ default DES settings only based on machine profiles. With this enhancement, in the following cases, Full Configuration sets an Azure catalog’s default DES settings directly based on the master image:
- If a machine profile isn’t selected
- If the profile specifies a Platform Managed Key (PMK)
November 2023
You can now create a Citrix Provisioning catalog using the Full Configuration interface and PowerShell (Drive the bus from Studio rather than the PVS Setup Wizard). This implementation provides the following advantages:
- A single unified console to manage both MCS and Citrix Provisioning catalogs.
- Have new features for Citrix Provisioning catalogs, such as identity management solutions, on-demand provisioning, and so on.
Currently, this feature is available only for Azure workloads. This feature is pretty cool and works well, but currently only supports initial creation of a Catalog. You must use existing processed for image updates etc via the PVS methdology.
Starting an existing VM on Azure is now faster than launching a new one, making it a more efficient choice to retain VMs across power cycles. In response to this change, Citrix has combined the options Retain VMs across power cycles and Retain system disk during power cycles into a single option Retain VM and system disk during power cycles. This means that when you select this option to reduce VM restart times by retaining system disks, your VMs are retained as well.
Once you choose a machine profile with Encryption at Host enabled during Azure machine catalog creation or management, only machine sizes that support this feature are displayed.
You can now view the following image information through the Template Properties of the machine catalog:
- Operating system
- Machine identity service
- Machine Creation Service storage
- Filepath for pagefile.sys for Azure deployments.
This enhancement provides better clarity on the image information and ensures that the administrators have all the information about the machine catalog in one place.
In Azure environments, a customer-managed resource tagged with all Citrix tags is detected as an orphaned resource. With this feature, if you add another tag CitrixDetectIgnore with value as true to that resource, then the resource is ignored while detecting orphaned resources.
After creating multiple VMs using MCS, the System Center Configuration Manager (SCCM) displayed only one VM on its console because of duplicated GUIDs. This issue is now resolved by adding a step in the image preparation. This step deletes the existing certificates and GUID information within master image. The step is enabled by default.
Not azure specific, but will impact Azure provisioned VMs.
With this feature, you can reset the identity information of active computer accounts that have identity-related problems. You can choose to reset only the machine password and trust keys, or reset all configuration of the identity disk. This implementation is applicable to both persistent and non-persistent machine catalogs. Currently, the feature is supported only for Azure and VMware virtualization environments.
In Azure environments, with this feature, you can now know whether encryption at host is enabled for a machine profile input (VM or template spec) using PowerShell commands.
Azure confidential computing VMs ensures that your virtual desktop is encrypted in memory and protected in use. With this feature, you can now use MCS to create a catalog with Azure confidential VMs. You must use the machine profile workflow to create such a catalog. You can use both VM and ARM template spec as a machine profile input.
With this feature, you can now change the memory and disk cache size of the Write-back cache (when MCSIO is enabled) using a PowerShell command without creating a new machine catalog. This implementation helps you to have the optimized cache configuration that is suitable for your business needs. This feature is applicable to:
- GCP and Microsoft Azure environments, and
- a non-persistent catalog with MCSIO enabled
In Azure environments, you can now create a Citrix Provisioning catalog enabled with customer-managed encryption key (CMEK) using the Full Configuration interface and PowerShell commands.
With this feature, in Azure environment, you can now copy tags specified in a machine profile to all the resources such as, multiple NICs and disks (OS disk, Identity disk, and write-back cache disk) of a new VM or an existing VM in a machine catalog.
The machine profile source can be a VM or an ARM template spec.
In Azure environments, you can create an MCS machine catalog that supports hibernation. Using this feature, you can suspend a VM, and then reconnect to the previous state of the VM when a user signs in again.
Previously, you could assign a specific drive letter to the write-back cache disk only by using a PowerShell cmdlet. You can now accomplish the same task using Full Configuration.
For Machine Creation Services-provisioned Azure machines, you can now change the following property settings using Full Configuration:
- Storage type
- Dedicated host group
- Azure Compute Gallery settings
When you change any of these settings, Full Configuration automatically identifies related settings and provides automatic synchronization or prompt messages requesting you to reselect related settings. This capability ensures consistent changes across associated settings, preventing potential configuration errors.
October 2023
With Full Configuration, you can now create Azure VMs with multiple NICs. A VM’s maximum NIC count is determined by the machine size setting while its actual NIC count allowed is defined by the machine profile setting
Creating empty machine catalogs now extends to non-MCS-provisioned machines, including:
- Virtual or blade machines provisioned using technologies other than Machine Creation Services.
- Physical machines not power managed by Citrix DaaS
- Remote PC Access machines
With this feature, you can now create machine catalogs without the need to add machines to them during catalog creation.
Previously, the NIC settings of the master image were not retained in the provisioned VMs. For example, if you configured the DNS settings on the master image, the provisioned VMs did not retain the configured DNS settings of the master image. With this feature, the provisioned VMs can now retain the NIC settings of the master image. The settings are retained even after a Windows update.
The filter driver is automatically installed if you do a fresh installation of VDA version 2308 or later on a Hyper-V (Azure) deployed machine through the MCS master image installations. However, currently, if you upgrade from an older version of VDA (version less than 2308) and want to install the filter driver, then you must select the checkbox Citrix HyperV Filter Driver on the Additional Components page while upgrading the VDA.
This feature is applicable to:
- Hyper-V VMs (including Azure and SCVMM)
- Persistent and non-persistent MCS machine catalogs
- Non-persistent MCS machine catalogs with MCSIO
- Master image with multiple NICs
With this feature, you can now detect the orphaned resources in your Azure deployment, enabling efficient resource management. After the orphaned resources are identified, you can take further action, bringing in more productivity and cost reduction.
When monitoring image update statuses for catalogs in Full Configuration, you can now view a new status Preparing image, in addition to the existing ones Fully updated, Partially updated, and Pending update.
September 2023
In Full Configuration, you can now create a machine catalog without immediate VM creation. With this feature, you can postpone VM creation until back-end hosts are fully prepared or VM provisioning is completed, gaining more flexibility in creating catalogs. Currently, this feature applies only to Machine Creation Services-provisioned catalogs.
In line with the closure of Microsoft Cloud Deutschland on October 29, 2021, Citrix removed the Azure Germany option from the host connection creation page.
August 2023
With Full Configuration, you can now enable VDA Upgrade for machine catalogs created through Azure Quick Deploy and then perform Upgrade VDA on them for immediate or scheduled upgrades.
An Azure only feature right now, you can now update properties of individual VMs in a persistent MCS machine catalog using a PowerShell command. This implementation helps you to manage individual VMs efficiently without updating the entire machine catalog.
As per Azure policy, you cannot upload or download more than five disks or snapshots at the same time with the same disk access object. With this feature, the limit of five concurrent upload or download is not enforced if you:
- Configure
ProxyHypervisorTrafficThroughConnector in CustomProperties, and
- Do not configure Azure policy to create Disk Accesses automatically for each new disk to use private endpoints.
Previously, the Windows operating system automatically assigned a drive letter to MCS I/O write-back cache disk. You can now assign a specific drive letter to MCS I/O write-back cache disk. This implementation helps to avoid conflicts between the drive letter of any applications that you use and the drive letter of MCS I/O write-back cache disk. This feature is applicable to only Windows operating system.
Not applicable when Azure temporary disk is used as write-back cache disk
Applicable drive letter for write-back cache disk: E to Z
When catalog creation fails, you can now retry the creation job. On failure, you can review troubleshooting information to help resolve the issues. The information describes the issues found and provides recommendations for resolving them. Failed catalogs are marked with an error icon. To see the details, go to the Troubleshoot tab of each catalog.
This one scrapes in on the Azure front, but only just. Citrix introduced an option to simplify the cleanup of stale Azure AD joined devices in Citrix DaaS. Previously, you had to run a custom PowerShell script to perform the task. Enabling this option grants host connections permission to automatically clean stale Azure AD joined devices.
You can now monitor image update statuses for non-persistent machine catalogs using a new column, Image Update. This column indicates whether images of a catalog are Fully updated, Partially updated, or Pending update.
To show the column in the Machine Catalogs table, follow these steps:
- In the Machine Catalogs node, select the Columns to Display icon in the action bar.
- Select Machine Catalog -> Image Status.
- Click Save.
Displaying the Image update column might degrade the console performance. We recommend displaying it only when necessary.
When selecting master images for machine catalogs, you can now quickly get the most up-to-date master image list using the Refresh option at the top right. Additionally, a Refresh option is available for machine profiles and host groups in Azure catalogs.
July 2023
In Azure environments, you can now get a list of orphaned resources that are created by MCS but are no longer used by MCS. This feature helps to avoid extra costs.
When creating a catalog of multi-session machines, you can now specify whether to make them persistent. For persistent multi-session machines, keep in mind that changes users make to the desktops are saved and accessible to all authorized users.
With this feature, stale Azure AD devices can be consistently deleted by assigning the Cloud Device Administrator role to the service principal and modifying the custom property of the hosting connection. If you do not delete the Azure stale AD devices, then the corresponding non-persistent VM stays in the initializing state until you manually remove it from the Azure AD portal.
When selecting master images for machine catalogs, you can now quickly get the most up-to-date master image list using the Refresh option at the top right. Additionally, a Refresh option is available for machine profiles and host groups in Azure catalogs.
June 2023
Previously, you only got the latest warnings and errors associated with a machine catalog. With this feature, you can now get a list of the historical warnings and errors of an MCS machine catalog. This list helps you to understand any issues with your MCS machine catalog and fix those issues.
When you provision Azure VMs, Full Configuration now preconfigures the following settings based on the selected machine profile:
- Host group
- Disk Encryption Set
- Availability Zone
- License Type
Traditionally, customers relied on the public internet to let Azure endpoints interact with resources in the environment. As a result, security concerns were raised because the public internet was accessed. With this feature, MCS enables network traffic to be routed through Citrix Cloud Connectors in the environment. This makes the environment safer because all Azure managed traffic originates from the customers environment. To enable this, add ProxyHypervisorTrafficThroughConnector in CustomProperties.
After you set the custom properties, you can configure Azure policies to have private disk access to Azure managed disks.
Azure Monitor Agent (AMA) collects monitoring data and delivers it to Azure Monitor. With this feature, you can provision MCS machine catalog VMs (persistent and non-persistent) with AMA installed as an extension. This implementation enables monitoring by uniquely identifying the VMs in monitoring data.
Currently, MCS supports only the machine profile workflow for this feature.
May 2023
In Azure, you can now use a VM or template spec as a machine profile input to convert a non-machine profile-based machine catalog to machine profile-based machine catalog. Existing VMs and new VMs added to the catalog take property values from the machine profile unless overwritten by explicit custom properties.
In Azure, you can now create an MCS machine catalog with double encryption. Double encryption is platform-side encryption (default) and customer-managed encryption (CMEK). If you are a high security sensitive customer who is concerned about the risk associated with any encryption algorithm, implementation, or a compromised key, you can opt for this double encryption. Persistent OS and data disks, snapshots, and images are all encrypted at rest with double encryption.
You can now use the PowerShell command Reset-ProvVMDisk to reset the OS disk of a persistent VM in an MCS created machine catalog. The feature automates the process of resetting the OS disk. For example, it helps in resetting the VM to its initial status of a persistent development desktop catalog created using MCS. Think of this as a reset back to the initial state of provisioning.
Again, not an MCS specific function, but impacts the process of settings up an environment for MCS. You can now get the following information while you create a host connection:
- List of all Citrix supported hypervisor plug-ins, including third party plugins
- Availability of hypervisor plug-in. If the availability status is false, possible reason might be that Cloud Connector is not installed
This feature helps you correctly set-up a resource location and thus, create a host connection.
Not quite MCS, but included as Autoscale and MCS provisioned workloads are so heavily entwined. A new option, Neither notify nor force user logoff, is now available on the Manage Autoscale -> User Logoff Notification page. With the option selected, Autoscale will neither force users to log off from machines in drain state nor notify users to log off and log on to a different machine.
The following capabilities have been added:
- Ability to display the Azure AD assigned security groups for VMs to join In Full Configuration, when you create Azure Active Directory joined VMs, an option, Join an assigned security group as a member, lets you add the Azure AD security group where the VMs reside to an assigned security group
- Support for renaming Azure AD security groups for VMs For VMs added to an Azure AD security group through Citrix DaaS, you can now rename the security group using Full Configuration -> Edit Machine Catalog. Renaming occurs after you save the change. Names of Azure AD security groups must not contain the following characters:
@ " \ / ; : # . * ? = < > | [ ] ( ) '.
In Full Configuration, you can now change networks for a connection. You can’t unassociate networks from a connection if they are in use.
Previously, Remove-ProvVM and Remove-ProvScheme PowerShell commands with ForgetVM parameter removed the VMs and machine catalogs from the Citrix database. However, the commands didn’t remove the tags from the resources. You had to individually manage the VMs and machine catalogs that weren’t deleted entirely from all the resources. With this feature, you can use:
Remove-ProvVM with ForgetVM parameter to remove VMs and tags created on the resources from a single VM or a list of VMs from a machine catalog.Remove-ProvScheme with ForgetVM parameter to remove a machine catalog from the Citrix database and tags created on the resources from an entire machine catalog.
This implementation helps in identifying orphaned resources that are created by MCS but no longer used by MCS. This feature is only applicable to persistent VMs.
April 2023
At power-on, the storage type of a managed disk might fail to change to the desired type due to a failure on Azure. Previously, in these scenarios, the VM would remain off with a failure message sent to you. With this feature, you can either choose to power on the VM even when storage cannot be restored to its configured type or choose to keep the VM powered off
You can now create an MCS machine catalog with encryption at host capability. Currently, MCS supports only the machine profile workflow for this feature. You can use a VM or a template spec as an input for a machine profile.
With this type of encryption, the server hosting the VM encrypts the data and the encrypted data flows through the Azure storage server. Therefore, this method of encryption encrypts data end to end.
With this feature, you can now modify the Azure AD dynamic security group name associated with a machine catalog. This modification helps you to make the Azure AD dynamic security group information stored in Azure AD identity pool object to be consistent with the information stored in Azure portal.
March 2023
The following capabilities have been added:
In Azure environments, you can now save storage costs by changing the storage type of existing VMs to a lower tier when the VMs are shut down. To do this, use the StorageTypeAtShutdown custom property.
This is release is allow to set these properties on an existing catalog rather than a new one as specified in an earlier release.
You can now add tenants and subscriptions that share the Azure Compute Gallery with the subscription of the connection. As a result, when creating or updating catalogs, you can select shared images from those tenants and subscriptions.
When changing catalog images, only images with the same OS type as the image in use are shown. With this enhancement, Citrix DaaS no longer supports changing the OS type for Azure catalogs after catalog creation.
February 2023
Previously, in Azure environments, you could share images only with shared subscriptions using Azure Compute Gallery. With this feature, you can now select an image in Azure Compute Gallery that belongs to a different shared subscription in a different tenant to create and update an MCS catalog.
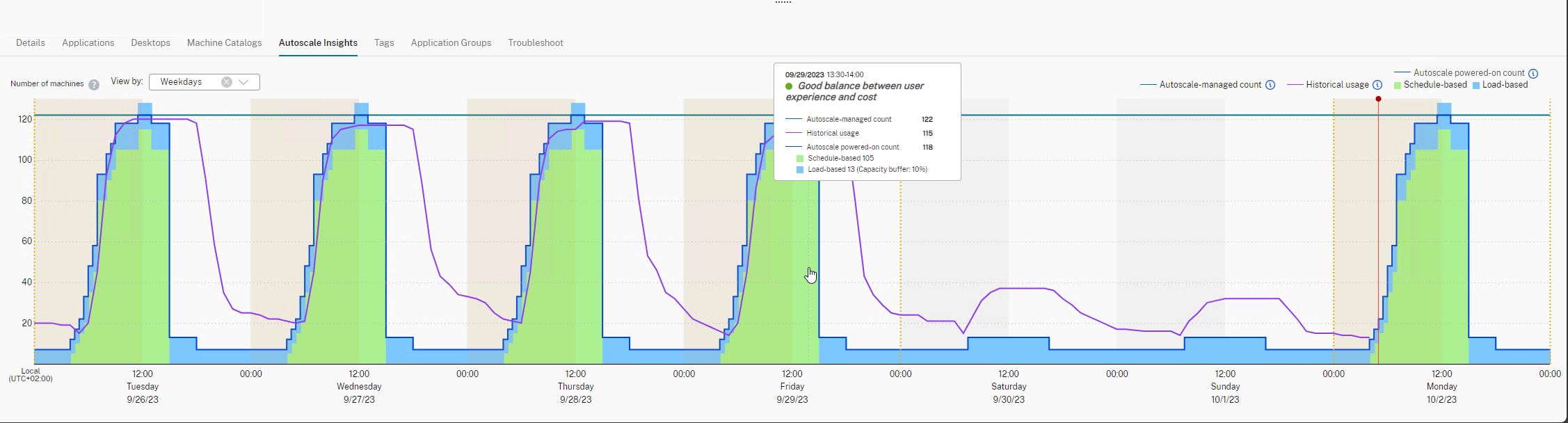
Whilst not MCS specific, Autoscale ties in nicely here.
Citrix updated the Control when Autoscale starts powering on tagged machines option to make it easy to understand. The option controls when Autoscale starts powering on tagged machines based on the percentage of the remaining capacity of untagged machines. When the percentage falls below the threshold (default, 10%), Autoscale starts powering on tagged machines. When the percentage exceeds the threshold, Autoscale goes into power-off mode
I am including this one because there are Azure specific considerations here.
You can now see GPU Utilization of AMD Radeon Instinct MI25 GPUs and AMD EPYC 7V12(Rome) CPUs on Monitor. Monitor already supports the NVIDIA Tesla M60 GPUs. GPU Utilization displays graphs with real-time percentage utilization of the GPU, the GPU memory, and of the Encoder and the Decoder to troubleshoot GPU-related issues on multi-session and single-session OS VDAs.
In Azure environments, you can now schedule a time slot for the configuration updates of the existing MCS provisioned machines using the PowerShell command Schedule-ProvVMUpdate. Any power on or restart during the scheduled time slot applies a scheduled provisioning scheme update to a machine. You can also cancel the configuration update before the scheduled time using Cancel-ProvVMUpdate.
You can schedule and cancel the configuration update of:
- A single or multiple VMs
- An entire catalog
Previously, MCS offered only locally-redundant storage. With this feature, zone-redundant storage is now an option in Azure, allowing you to select a storage type depending on what type of redundancy you want to use. Zone-redundant storage replicates your Azure managed disk across multiple availability zones, which allows you to recover from a failure in one zone by utilizing the redundancy in others
January 2023
A new option, Enable storage cost saving, is now available on the Disk Settings page when you create or update Azure catalogs. The option saves storage costs by downgrading to Standard HDD for the storage disk and the write-back cache disk when the VM shuts down. The VM switches to its original settings on restart.
This is awesome to see come to life - more cost savings
The option to retain VMs in hypervisors or cloud services is now available only to persistent VMs
December 2022
You can now delete VM objects in MCS without having access to the hypervisor. When deleting a VM or provisioning scheme, MCS needs to remove tags so that the resources are no longer tracked or identified. Previously, if the hypervisor could not be accessed, the tag removal failures were ignored. With this feature, if the hypervisor is not accessible while using the Remove-ProvVM command the tag removal will fail, but by using the PurgeDBOnly option, you can still delete the VM resource object from the database.
November 2022
When creating an MCS catalog in Full Configuration, you can now annotate its master image. This was previously only available for updates to an existing Catalog, and whilst not Azure specific, definitely adds value to Azure deployments.
You can now save storage costs by switching the storage type of a managed disk to a lower tier when you shut down a VM. To do this, use the StorageTypeAtShutdown custom property. The storage type of the disk changes to a lower tier (as specified in the StorageTypeAtShutdown custom property) when you shut down the VM. After you power on the VM, the storage type changes back to the original storage type (as specified in StorageType or WBCDiskStorageType custom property)
Previously, in Azure environments, you could use Request-ProvVMUpdate to update the ServiceOffering custom property of an MCS provisioned machine. Now, you can also update the machine profile and the following custom properties:
StorageTypeWBCDiskStorageTypeIdentityDiskStorageTypeLicenseTypeDedicatedHostGroupIdPersistWBCPersistOsDiskPersistVm
October 2022
When creating a catalog using an Azure Resource Manager master image, you can now use a machine profile and a host group at the same time. This is useful in scenarios where you want to use trusted launch for improved security and at the same time run the machines on dedicated hosts
September 2022
You can create machine catalogs enabled with Trusted launch, and use the SupportsTrustedLaunch property of the VM inventory to determine the VM sizes that support Trusted launch.
Trusted launch is a seamless way to improve the security of Generation 2 VMs. Trusted launch protects against advanced and persistent attack techniques.
Previously, in Azure environments, you could only select an image within your subscription to create a machine catalog. With this feature, you can now select an image in Azure Compute Gallery (formerly Shared Imaged Gallery) that belongs to a different shared subscription to create and update MCS catalogs.
August 2022
There is now a pre-flight check to assess whether the creation of a machine catalog will be successful based on the Azure availability zone specified in the custom property and the host group’s zone. Catalog creation fails if the availability zone custom property does not match the host group’s zone.
A host group is a resource that represents a collection of dedicated hosts. A dedicated host is a service that provides physical servers that host one or more virtual machines. Azure availability zones are physically separate locations within each Azure region that are tolerant to local failures.
In Azure environments, you can now avoid potential confusion with the page file location. MCS now determines the page file location when you create the provisioning scheme during image preparation. This calculation is based on certain rules. Features like ephemeral OS disk (EOS) and MCS I/O have their own expected page file location and are exclusive to each other.
If you decouple image preparation from provisioning scheme creation, MCS correctly determines the page file location.
While creating a catalog in an Azure environment, you can now specify the page file setting, including its location and the size, using PowerShell commands. This overrides the page file setting determined by MCS. You can do this by running the New-ProvScheme command with the following custom properties:
PageFileDiskDriveLetterOverride: Page file location disk drive letterInitialPageFileSizeInMB: Initial page file size in MBMaxPageFileSizeInMB: Maximum page file size in MB
When using an ARM template spec as a machine profile to create a machine catalog, you can now add Azure VM extensions to the VMs in the catalog, view the list of supported extensions, and remove extensions you added. Azure VM extensions are small applications that provide post-deployment configuration and automation tasks on Azure VMs. For example, if a VM requires software installation, antivirus protection, or the ability to run a script inside it, you can use a VM extension
You can now create provisioning schemes using ephemeral OS disk on Windows with trusted launch. Trusted launch is a seamless way to improve the security of generation 2 VMs. It protects against advanced and persistent attack techniques by combining technologies that can be independently enabled like secure boot and virtualized version of trusted platform module (vTPM
July 2022
Again, whilst not Azure specific, this has implications on Azure capability. Dynamic session timeouts now support single-session OS machines. A delivery group with at least one VDA of version 2206 or later is required. Ensure that those VDAs have registered with Citrix Cloud at least once
Whilst not Azure specific, this is still important for Azure based deployments. A new feature is now available in User Logoff Notifications (formerly Force User Logoff) in Autoscale. The feature provides functionality to send logoff reminders to users without forcing them to log off. Doing that avoids potential data loss caused by forcing users to log off from their sessions
Using the Full Configuration interface, the Linux OS license type can be selected when creating Linux VM catalogs in Azure. There are two choices for bring-your-own Linux licenses:
- Red Hat Enterprise Linux
- SUSE Linux Enterprise Server
Previously, only VMs could be used as machine profiles. ARM template specs can be used as machine profiles when creating Azure machine catalogs. This allows for taking advantage of Azure ARM template features such as versioning. To ensure that the selected spec is configured correctly and contains required configurations, Citrix perform validation tasks on it. If the validation fails, a different machine profile must be selected
Validation of an ARM template spec to make sure that it can be used as a machine profile to create a machine catalog is now available. There are two ways to validate the ARM template spec:
- Using the Full Configuration management interface
- Using PowerShell
June 2022
When using the Full Configuration management interface to select a machine profile for the VMs to inherit configurations from, an ARM template spec can now be selected
The network setting for an existing provisioning scheme can be altered so that the new VMs are created on the new subnetwork. Use the parameter -NetworkMapping in the Set-ProvScheme command to change the network setting. Only the newly provisioned VMs from the scheme will have the new subnetwork settings. Subnetworks must be under the same hosting unit
The region name information for an Azure VM, managed disks, snapshots, Azure VHD, and ARM template can now be displayed. This information is displayed for the resources on the master image when a machine catalog is assigned
While creating an Azure catalog with a machine profile, property values from the ARM template spec or VM, whichever is used as a machine profile, can be set if the values are not explicitly defined in the custom properties. The properties affected by this feature are:
- Availability zone
- Dedicated Host Group Id
- Disk Encryption Set Id
- OS type
- License type
- Service Offering
- Storage type
If some of the properties are missing from the machine profile and not defined in the custom properties, then the default value of the properties takes place wherever applicable. See Create a machine catalog using an Azure Resource Manager image for more information
May 2022
Set-ProvServiceConfigurationData can now be run using Remote PowerShell SDK to apply settings on all applicable parameters. The following list of settings are supported with Set-ProvServiceConfigurationData:
- Change Image Preparation Timeout:
Set-ProvServiceConfigurationData -Name "ImageManagementPrep_PreparationTimeout" -value 60
- Skip Enable DHCP:
Set-ProvServiceConfigurationData -Name ImageManagementPrep_Excluded_Steps -Value EnableDHCP
- Skip Microsoft Windows KMS Rearm:
Set-ProvServiceConfigurationData -Name ImageManagementPrep_Excluded_Steps -Value OsRearm
- Skip Microsoft Office KMS Rearm:
Set-ProvServiceConfigurationData -Name ImageManagementPrep_Excluded_Steps -Value OfficeRearm
- Disable preparation VM auto shutdown:
Set-ProvServiceConfigurationData –Name ImageManagementPrep_NoAutoShutdown –Value true
- Disable domain injection:
Set-ProvServiceConfigurationData –Name DisableDomainInjection –Value true
MCS now supports Azure Stack HCI provisioning through Microsoft System Center Virtual Machine Manager (SCVMM). Azure stack HCI clusters can be managed with existing tools including SCVMM
April 2022
Full Configuration now shows updates on catalog creation and updates. This displays the overview of the creation and update process, view the history of steps performed, and monitoring of both the progress and running time of the current step
An Azure Active Directory joined identity type is now available in Machine Identities when creating a Catalog. With that identity type, MCS can create machines that are joined to Azure Active Directory. An extra option is available, Enroll the machines in Microsoft Intune, to enroll the machines in Microsoft Intune for management.
For information about requirements and considerations related to Azure Active Directory join, see Azure Active Directory joined detail
A Hybrid Azure Active Directory joined identity type is now available in Machine Identities when creating a Catalog. With that identity type, MCS can create hybrid Azure Active Directory joined machines. Those machines are owned by an organization and signed into with an Active Directory Domain Services account that belongs to that organization. Additional information is available for Hybrid Azure Active Directory joined device provisioning
In addition to images, Azure trusted launch is now available for snapshots. If selecting a snapshot with trusted launch enabled, using a machine profile is mandatory. A machine profile with trusted launch enabled must be selected
You will now get an error if you set the New-ProvScheme parameters in unsupported hypervisors during machine catalog creation or update Set-ProvScheme parameters after machine catalog is created
Not Azure and MCS specific, but will impact design decisions. Resource Location limits for single-session VDAs and multi-session VDAs are now increased to 10000 and 1000 respectively
Citrix DaaS now prevents virtual machines from being shut down by the broker when the zone that the machines are in experiences an outage. The machines automatically become available for connections when the outage ends. You don’t have to take any action to make the machines available after the outage
A couple of small changes to Autoscale
- Renamed Restrict Autoscale to Autoscaling Tagged Machines to make it easy to understand
- Added a new option, Control when Autoscale starts powering on tagged machines. The option lets you control when Autoscale starts powering on tagged machines based on the usage of untagged machines
Set-ProvScheme changes the template (provisioning scheme) associated with the catalog, but does not affect existing machines. Using Request-ProvVMUpdate command, you can now apply the current provisioning scheme to an existing machine (or set of machines). Currently, the property update supported by this feature is ServiceOffering.
This is very handy when you need to change exsting VM sizes within an existing catalog
March 2022
MCS now supports Azure trusted launch in the Full Configuration management interface. If you choose to select an image with trusted launch enabled, using a machine profile is mandatory. This machine profile must have trusted launch enabled
Whilst not Azure specific, this is heavily Azure focused and will impact MCS capability. IPS simplifies the management of images across platforms. This feature is useful for managing images between an on-premises Resource Location and the public cloud
February 2022
There are two sets of permissions required for security requirements and to minimize risk
- Minimum permissions: This set of permissions gives better security control. However, new features that require additional permissions will fail because of using minimum permissions
- General permissions: This set of permissions does not block you from getting new enhancement benefit
A new option added: Use non-persistent write-back cache disk, to the Machine Catalog Setup > Disk Settings page of the Manage > Full Configuration interface. Select that option if you do not want the write-back cache disk to persist for the provisioned VMs. With the option selected, the VM’s temporary disk is used to host the write-back cache disk if the temporary disk has sufficient space. Doing this reduces cost
Using the Full Configuration management interface, you can now change the following settings after creating a catalog:
- Machine size
- Availability zones
- Machine profile
- Windows licenses
On the Machine Catalogs node, select the catalog and then select Edit Machine Catalog in the action bar.
Note: These changes only impact newly reprovisioned machines. Previously created machines remain the same
It is now supported to store the Azure ephemeral OS disk either on cache disk or temporary disk for an Azure-enabled virtual machine. You can read more on Azure Ephemeral Disks with MCS here
January 2022
Using the Full Configuration management interface, there is now an option to specify the date after which the application secret expires. This is useful as it will prevent being surprise locked out of Azure
- For service principals created manually in Azure, you can directly edit the expiration date on the
Edit Connection > Connection Properties page
- For first-time edits of the expiration date for service principals created through Full Configuration on your behalf, go to
Edit Connection > Edit settings > Use existing. You can make subsequent edits on the Edit Connection > Connection Properties page
December 2021
Previously, PowerShell was the only choice to create machines that use ephemeral OS disks. There is a new option to select “Azure ephemeral OS disk” in the Machine Catalog Setup > Storage and License Types page
November 2021
When updating an MCS-created catalog, notes can be added to assist with tracking changes. Each time the catalog is updated, a note-related entry is created whether or not a prescriptive note is added. If the catalog is updated without adding a note, the entry appears as null (-).
To view note history for the image, select the catalog, click Template Properties in the lower pane, and then click View note history.
This is not Azure specific, but I am adding this as it’s very handy and long awaited
When creating a machine catalog, you can now view purchase plan information for master images originated from Azure Marketplace images
October 2021
Citrix added a setting Retain VMs across power cycles to the Machine Catalog Setup > Disk Settings page of the Full Configuration management interface. The setting lets you preserve a provisioned VM when power cycling in Azure environments.
Be wary of cost implications associated with persistent OS disks
Citrix introduced the Update Machines option for persistent MCS catalogs in the Full Configuration management interface. The option lets customers manage the image or template the catalog uses. When updating a persistent catalog, consider the following:
Only machines you add to the catalog later are created using the new image or template. We do not roll out the update to existing machines in the catalog
This is signifcant given the previous method wasn’t easily understood for those not in bed with PowerShell
Citrix added an option, Use a host group, to the Machine Catalog Setup > Master Image page of the Full Configuration management interface. The option lets customers specify which host group they want to use when provisioning VMs in Azure environments
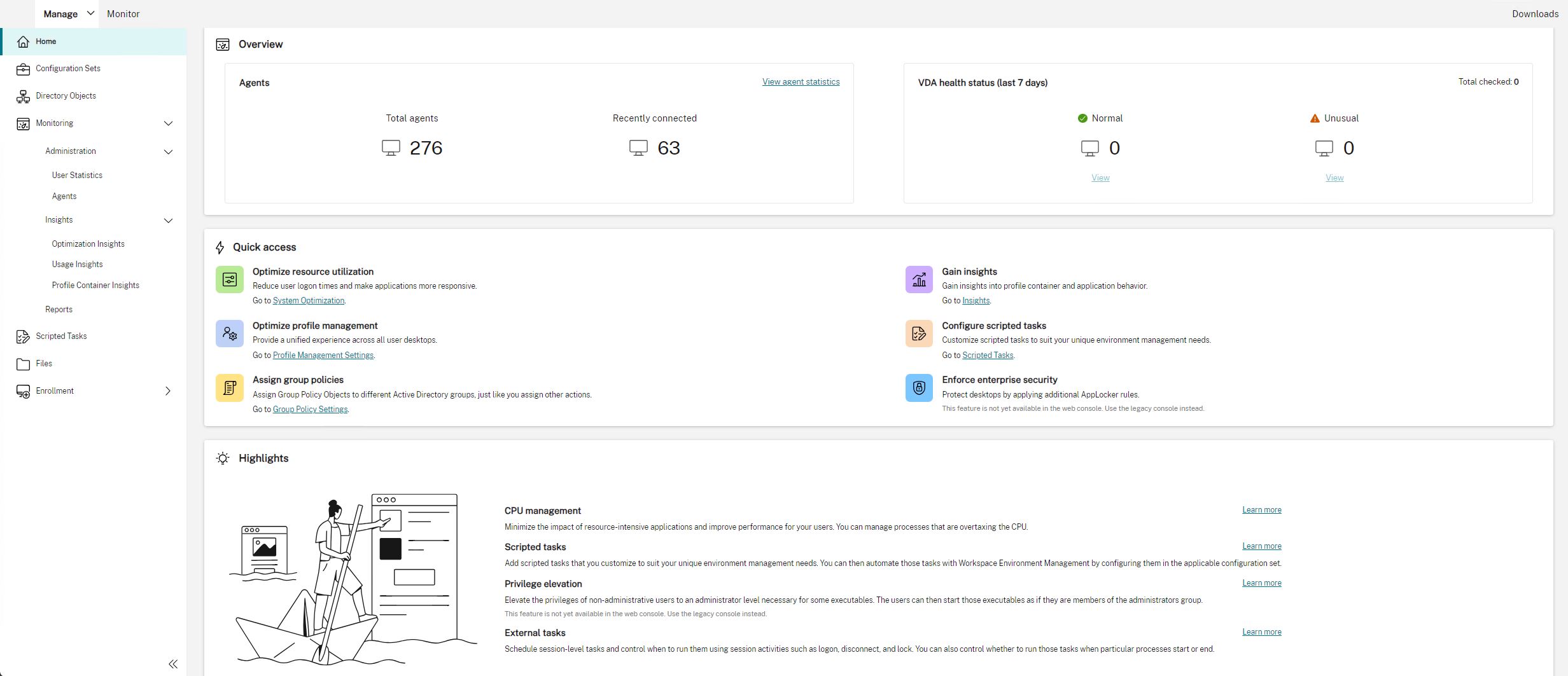
A machine catalog can now be bound to a Workspace Environment Management configuration set on creation. Customers can also choose to bind the catalog after they create the catalog.
Whilst not specifically an MCS feature, it is an enhancement that MCS will consume, so it makes the list of goodies
September 2021
Change details associated with catalog updates can now be added via PowerShell using the masterImageNote attribute. This functionality is useful for administrators who want to add descriptive labels when updating an image used by a catalog.
Hopefully this lands in the GUI shortly for general consumption
Citrix Virtual Apps and Desktops service supports AVS, the Azure VMware Solution. Customers can leverage the Citrix Virtual Apps and Desktop service to use AVS for provisioning workloads in the same they would using vSphere in on-premises environments
Customers can now use the same resource group for updating and creating catalogs in the Citrix Virtual Apps and Desktops Service. This process:
- Applies to any resource group that contains one or more machine catalogs
- Supports resource groups that are not created by Machine Creation Services
- Creates the VM and associated resources
- Deletes resources in the resource group when the VM or the catalog is removed
You can display information for an Azure VM, OS disk, snapshot and gallery image definition. This information is displayed for resources on the master image when a machine catalog is assigned. Use this functionality to view and select either a Linux or Windows image
Destail: Citrix added an identity type, Non-domain-joined, to the Machine Catalog Setup > Machine Identities page of the Full Configuration management interface. With this identity type, MCS can create machines that are not joined to any domain
Support for using a machine profile when deploying MCS workloads in Azure
This option lets you specify which machine profile you want the image to inherit the configuration from when creating VMs in Azure environments. The image can inherit the following configurations from the selected machine profile:
- Accelerated networking
- Boot diagnostics
- Host disk caching (OS and MCSIO disks)
- Machine size (unless otherwise specified),
- Tags placed on the VM
This is awesome. If you have needed to implement my Accelerated Networking scripts, then consider using this feature instead
Support for Windows Server 2022
Requires minimum VDA 2106
August 2021
You can now select different storage types for virtual machines in Azure environments using MCS
In the Full Configuration management interface, when creating an MCS catalog, you can now select the storage type for the write-back cache disk. Available storage types include: Premium SSD, Standard SSD, and Standard HDD
June 2021
When creating a machine catalog, you can now access images from the Azure Shared Image Gallery on the Master Image screen
Always use standard SSD for an identity disk to reduce cost in Azure environments
Machine catalogs use the standard SSD storage type for identity disks. Azure standard SSDs are a cost-effective storage option optimized for workloads that need consistent performance at lower IOPS levels.
You can read more about the benefits of this change here and utilise the provided scripts to convert existing deployments
May 2021
Previously, PowerShell was the only choice to provision machines into a specific Availability Zone in Azure environments.
When using Studio to create a machine catalog, you can now select one or more Availability Zones into which you want to provision machines. If no zones are specified, Machine Creation Services (MCS) lets Azure place the machines within the region. If more than one zone is specified, MCS randomly distributes the machines across them
Citrix Virtual Apps and Desktops service supports Azure ephemeral disk. An ephemeral disk allows you to repurpose the VM cache to store the OS disk for an Azure-enabled virtual machine.
Ephemeral OS disks require that your provisioning scheme use managed disks and a Shared Image Gallery.
This enhancement changes the default values for Absolute Simultaneous actions for the hosting connection to 500, and Maximum new actions per minute for the hosting connection to 2,000. No manual configuration tasks are required to take advantage of this enhancement
April 2021
MCS I/O now supports machine catalog creation for VMs that do not have temporary disks or attached storage
Support for Azure Gen2 images
You can now provision a Gen2 VM catalog by using either a Gen2 snapshot or a Gen 2 managed disk to improve boot time performance
Disabling table storage accounts
Machine Creation Services (MCS) no longer creates table storage accounts for catalogs that use managed disks when provisioning VDAs on Azure
Eliminating locks in storage accounts
When creating a catalog in Azure using a managed disk, a storage account is no longer created. Storage accounts created for existing catalogs remain unchanged. This change is applicable for managed disks only. For unmanaged disks, there is no change in the existing behavior. Machine Creation Services (MCS) continues creating storage accounts and locks
Studio adds a setting called Customer-managed encryption key to the Machine Catalog Setup > Disk Settings page. The setting lets you choose whether to encrypt data on the machines to be provisioned in the catalog
March 2021
Azure dedicated hosts allow you to provision virtual machines on hardware dedicated to a single customer. While using a dedicated host, Azure ensures that your virtual machines would be the only machines running on that host. This provides more control and visibility to customers thereby ensuring they meet their regulatory or internal security requirements.
A pre-configured Azure host group, in the region of the hosting unit, is required when using the HostGroupId parameter. Also, Azure auto-placement is required.
When using Azure dedicated hosts, selecting the Azure Availability Zone has no effect. The virtual machine is placed by the Azure auto-placement process.
Citrix Virtual Apps and Desktops service supports customer-managed encryption keys for Azure managed disks. With this support you can manage your organizational and compliance requirements by encrypting the managed disks of your machine catalog using your own encryption key
You can now provision machines into a specific availability zone in Azure environments. With this functionality You can specify one or multiple Availability Zones on Azure. Machines are nominally equally distributed across all provided zones if more than one zone is provided The virtual machine and the corresponding disk are placed in the specified zone (or zones)
Citrix Virtual Apps and Desktops service supports Azure Shared Image Gallery as a published image repository for MCS provisioned machines in Azure. Administrators have the option of storing an image in the gallery to accelerate the creation and hydration of OS disks. This process improves the boot and application launch times for non-persistent VMs
February 2021
You can now provision managed disks using Gen2 VMs in Azure environments to improve boot time performance
Citrix Managed Azure is now available in the following Citrix Virtual Apps and Desktops service editions: Standard for Azure, Advanced, Premium, and Workspace Premium Plus
Studio now provides you an option to place master images in Azure Shared Image Gallery (SIG). SIG is a repository for managing and sharing images. It lets you make your images available throughout your organization.
Citrix recommend that you store a master image in SIG when creating large non-persistent machine catalogs because doing that enables faster reset of VDA OS disks
Studio now lets you control whether to retain system disks for VDAs during power cycles. Ordinarily, the system disk is deleted on shutdown and recreated on startup. This ensures that the disk is always in a clean state but results in longer VM restart times. If system writes are redirected to the cache and written back to the cache disk, the system disk remains unchanged.
To avoid unnecessary disk recreation, use the Retain system disk during power cycles option, available on the Machine Catalog Setup > Disk Settings page. Enabling the option reduces VM restart times but increases your storage costs. The option can be useful in scenarios where an environment contains workloads with sensitive restart times
Previously, PowerShell was your only choice to create a catalog with persistent write-back cache disk. You can now use Studio to control whether the write-back cache disk persists for the provisioned VMs in Azure when you are creating a catalog. If disabled, the write-back cache disk is deleted during each power cycle to save storage costs, causing any data redirected to the disk to be lost.
To retain the data, enable the Use persistent write-back cache disk option, available on the Machine Catalog Setup > Disk Settings page.
January 2021
Details: Citrix Virtual Apps and Desktops service supports Azure Shared Image Gallery as a published image repository for MCS provisioned machines in Azure. Administrators have the option of storing an image in the gallery to accelerate the creation and hydration of OS disks from the master image. This process improves the boot and application launch times for non-persistent VMs
December 2020
Details: Studio now adds support for standard SSD disk type. Azure standard SSDs are a cost-effective storage option optimized for workloads that need consistent performance at lower IOPS levels
October 2020
Details: Direct upload eliminates the need to attach an empty managed disk to a virtual machine. Directly uploading to an Azure managed disk simplifies the workflow by enabling you to copy an on-premises VHD directly for use as a managed disk. Supported managed disks include Standard HDD, Standard SSD, and Premium SSD
Details: You can now create and use a single Azure resource group for updating and creating catalogs in Citrix Virtual Apps and Desktops. This enhancement applies to both the full scope and narrow scope service principals. The previous limit of 240 VMs per 800 managed disks per Azure Resource Group has been removed. There is no longer a limit on the number of virtual machines, managed disks, snapshots, and images per Azure Resource Group
September 2020
Support for a new machine type
Details: This release adds support for the NV v4 and the DA v4 series of AMD machines, when configuring Premium Disks for a machine catalog
August 2020
Details: This release supports improved boot performance for Citrix Cloud implementations using Azure when MCSIO is enabled. With this support, you can retain the system disk. This provides the following advantages:
- VMs and applications now boot and launch with performance similar to how the golden image is served
- Reduction in API quota consumption, deleting and creating the system disk, and state transition delay caused when you delete a VM
]]>